Table of Contents
TLDR
Microsoft suspended the developer accounts behind VeraCrypt, WireGuard and Windscribe without warning. The Microsoft developer account lockout stopped all three projects from signing Windows drivers or shipping updates. Tens of millions of Windows users can’t get patches right now. Microsoft VP Scott Hanselman stepped in after public outcry and says fixes are underway. But the damage is already done, and it raises proper questions about platform dependence.
What Caused the Microsoft Developer Account Lockout?
In early April 2026, developers behind three major open source security tools logged in to find their accounts frozen. No emails. No warnings. Just a wall of “access restricted” messages.
VeraCrypt’s lead developer Mounir Idrassi discovered the block first. He posted on SourceForge that Microsoft had terminated his account with zero explanation. He’d used that same account for years to sign Windows drivers and the VeraCrypt bootloader.
Days later, WireGuard creator Jason Donenfeld hit the same problem. He’d been modernising WireGuard’s Windows code for weeks. When he tried to submit the update, his account was dead. This would have been the first big WireGuard update on Windows in nearly four years.
Then Windscribe, a well-known VPN provider, confirmed they’d been locked out too. They’d held a verified account for over eight years. Their team had spent a month trying to get it sorted, with no luck.
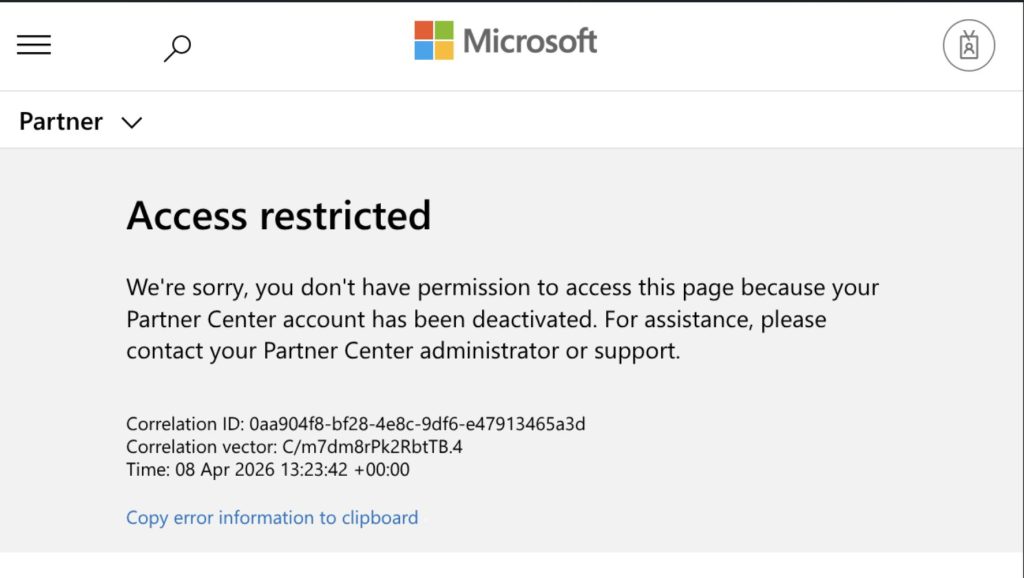
The “Access restricted” error shown to WireGuard developer Jason Donenfeld when attempting to access Microsoft Partner Center.
The Windows Hardware Program Verification Mess
Here’s the thing. Microsoft runs a programme called the Windows Hardware Program. It lets developers sign kernel-level drivers. Without that signature, Windows blocks the driver from loading. Simple as that.
Back in October 2023, Microsoft introduced mandatory account verification for everyone on the programme. Developers had 30 days to upload a government-issued ID. Fail to verify and your account gets suspended.
Microsoft VP Scott Hanselman said the company had been sending emails about this since October 2025. But the affected developers tell a different story. Donenfeld said he checked every inbox, every spam folder, every mail log. Nothing. Idrassi said the same. Neither got a single warning.
Donenfeld went further. He actually completed the verification process through Microsoft’s third-party provider. The provider marked him as verified. His account stayed frozen anyway.

The verification rejection notice received by VeraCrypt developer Mounir Idrassi, stating no appeals are available
Why This Microsoft Developer Account Lockout Actually Matters
This isn’t just paperwork gone wrong. The consequences are real and pretty scary.
VeraCrypt users who’ve encrypted their entire system could face boot failures after July 2026. That’s because Microsoft is revoking the certificate authority used to sign VeraCrypt’s bootloader. Idrassi needs account access to apply a new signature. Without it, he said it could be a “death sentence” for VeraCrypt on Windows.
WireGuard sits beneath loads of popular VPN services. Mullvad, Proton, Tailscale and others all rely on its code. Donenfeld pointed out that if a critical vulnerability turned up right now, Windows users would be completely exposed. He can’t patch anything.
Linux and macOS users aren’t affected. The open source security tools can still push updates on those platforms. But Windows is where most users are, and that’s exactly where updates can’t reach.
Platform Dependence and Windows Driver Signing Risks
This whole episode highlights a problem that security professionals have worried about for years. Critical open source security tools depend entirely on a single company’s infrastructure to reach their users.
Windows driver signing is non-negotiable. If Microsoft pulls the plug on your account, your software can’t run at kernel level. Your bootloader won’t load. Your VPN driver won’t install. There’s no workaround.
MemTest86, the memory testing tool, reportedly got caught up in the same sweep. So this isn’t limited to privacy and encryption software. Any developer relying on Microsoft’s Partner Center for Windows driver signing could be one bureaucratic mishap away from losing access.
Expert Commentary
William Fieldhouse, Director of Aardwolf Security Ltd, commented: “This incident is a proper wake-up call for anyone running security-critical software on Windows. When a single platform holder can freeze updates to tools used by millions, that’s a supply chain risk that deserves serious attention. Organisations should be reviewing their dependence on any single vendor’s signing infrastructure as part of their broader security posture.”
Microsoft’s Response and the 60-Day Wait
After the story blew up on social media and tech news sites, Microsoft VP Scott Hanselman stepped in personally. He said on X that he’d spoken to both Donenfeld and Idrassi and that everything was being sorted out.
Hanselman pushed back a bit, though. He tweeted that sometimes these things come down to checking your emails and verifying your accounts. Not every complaint about Microsoft is justified, he suggested.
But there’s a catch. Before Hanselman got involved, the official appeals process gave developers a 60-day wait for a response. Sixty days. For software that protects millions of people. Windscribe had already been battling Microsoft support for over a month with nothing to show for it.
That gap between automated enforcement and actual human support is where the real damage sits. By the time someone important notices, the lockout has already been active for weeks.
What Security Teams Should Take From This
If you manage security for an organisation, this story should get your attention. The open source security tools your team depends on can be cut off from updates by forces completely outside anyone’s control. Think about your VPN infrastructure. If your provider uses WireGuard under the bonnet, a missed patch window could leave you exposed. Same goes for disk encryption. VeraCrypt is brilliant software, but if it can’t get signed for Windows, your encrypted endpoints are stuck on old code.
This is why working with the best penetration testing company matters. A good testing partner will flag these kinds of supply chain risks before they become incidents.
Microsoft Developer Account Lockout: A Warning Shot
The Microsoft developer account lockout of April 2026 will likely be resolved soon, thanks to public pressure. Hanselman’s intervention suggests Microsoft knows it messed up. But the underlying problem remains.
Open source projects that protect millions of people shouldn’t be one unread email away from losing their ability to ship updates. The Windows driver signing system gives Microsoft enormous power over third-party security tools. And until that changes, every organisation using these tools carries a risk they probably haven’t accounted for.
The Microsoft developer account lockout isn’t just a story about bureaucracy. It’s a reminder that your security stack is only as reliable as the weakest link in its supply chain.
At Aardwolf Security, we regularly uncover outdated or unpatched third-party software during our network penetration assessments. Tools like VeraCrypt and WireGuard often sit on endpoints without anyone tracking their update status. Situations like this Microsoft lockout make that gap even wider. If you want to know what’s lurking on your network, get in touch for a penetration test quote and let us help you find the blind spots before someone else does.